Linux 7.0: One Bash Script, One Weekend, 23 Years of Kernel Bugs
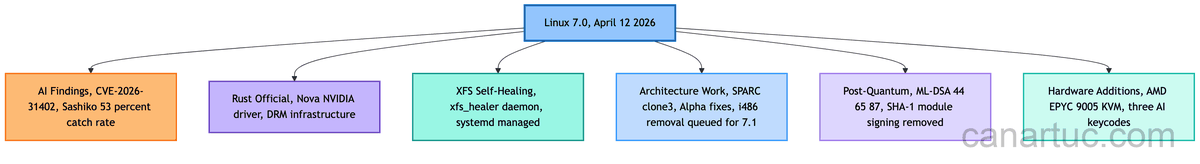
Table of Contents
- A Bash Script’s Weekend
- AI Reviewing Patches Is the New Normal
- Rust Won. Both Sides Quit.
- New Rules for AI-Written Code
- Linux 7.0 Hardware Legacy: From XFS Self-Healing to SPARC Survival
- Linux 7.0 Gave AI Three Physical Keys
- One Linux 7.0 Release, Four Technical Shifts
- The Next 23-Year Bug
- Frequently Asked Questions
Have you ever walked past that noodle shop on your street, the one that has been open for twenty-three years, and wondered if their gas valve was installed backwards the entire time?
Every day they fire up the stove, stir-fry, boil noodles. Nobody notices anything wrong. Then one day an intern chef twists a valve and realizes the whole kitchen has been playing with fire.
Inside the Linux kernel, there was a valve like that. Open for twenty-three years.
A Bash Script’s Weekend
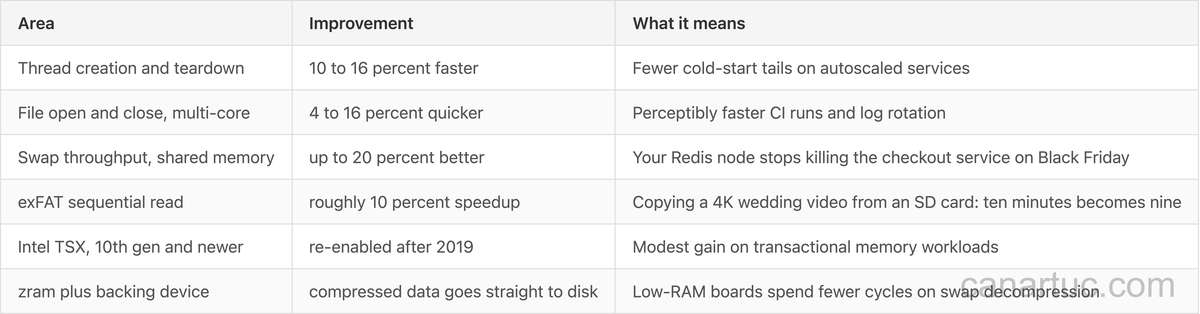
Nicholas Carlini is a security researcher. He wrote a bash script so simple it was almost embarrassing. Loop through kernel source files, feed them to Claude Opus 4.6, and ask: “Pretend you are in a CTF. What can you break?”
The script ran for months. Every time it was just noise. The “vulnerabilities” the model pointed out were either false positives or did not exist at all.
One Friday night Carlini was not watching the screen. The script ran on its own.
Then it stopped.
The result made Carlini drop everything. Claude had found a hole hidden in Linux’s network file sharing code. That same code runs on your company’s file server, on hospital storage devices, and on a significant slice of AWS, GCP, and Azure instances. Your kid’s school cloud drive probably uses it too.
With this bug, an intern on day one, connected to the office guest Wi-Fi, could run a few lines of script and take over the entire file server.
Take over means reading HR’s salary spreadsheet.
Carlini checked the commit history. The hole was cut in March 2003. Git did not even exist yet. For two decades, every Linux-based storage appliance shipped with this bug baked in.
Later he told an audience at the [un]prompted security conference: “I have never found one of these in my life before. This is very, very, very hard.”
But his script was not clever. It was just cheap.
One person, one week of compute. Pocket change in economic terms.
Three weeks later Linus Torvalds tagged Linux 7.0. In his release email he wrote a line that sounded like a shrug: “I suspect it is a lot of AI tool use that will keep finding corner cases for us for a while, so this may be the ’new normal’ at least for a while.”
April 12, 2026, a Sunday. Linux 7.0 shipped. This is the story of what arrived with it, and who put it there.
AI Reviewing Patches Is the New Normal
Greg Kroah-Hartman runs the stable Linux kernel. He is Linus’s number two. He also runs the kernel’s security inbox, which means for years he opened his email to find mostly garbage.
He called it “AI slop.” Generated reports, no real bug, wrong file, wrong line, wrong everything. He had a folder for it.
Then one morning in late February, the folder stopped filling.
Real reports started coming in instead. Precise line numbers. Reproducers that actually reproduced. Root causes that held up. He told The Register in March: “Months ago, we were getting what we called AI slop. Something happened a month ago, and the world switched. Now we have real reports.” He also said: “We don’t know. Nobody seems to know why.”
Either every frontier model suddenly learned to read C in the same month, or a critical mass was crossed.
Greg did what a maintainer does. He wrote documentation.
Ahead of 7.0-rc7, he pushed a pull request updating security-bugs.rst. That file tells security researchers how to submit a vulnerability. The updated version was written for language models. Which maintainer handles which subsystem, what a well-formed report looks like, which fields an automated pipeline should include.
The kernel’s security intake is now dual-use. Humans and agents file through the same lane.
Another team was watching commits, not CVEs.
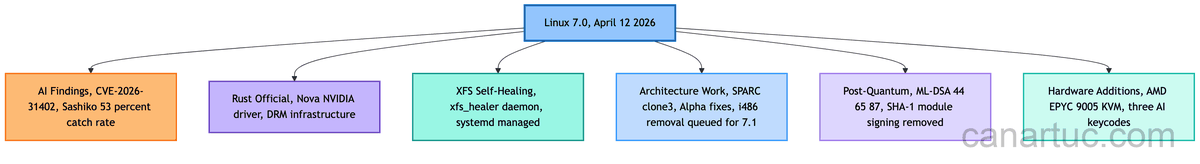
Google’s Roman Gushchin launched Sashiko, named after a Japanese embroidery technique, written in Rust (which is itself a small joke you will understand in a minute). Sashiko reads every patch posted to LKML. Against a benchmark of 1,000 real-world patches, it catches 53 percent of bugs that were later found.
Every single one had been missed by human reviewers.
When asked about the number, Gushchin said: “Some might say 53 percent is not that impressive. One hundred percent of these issues were missed by human reviewers.”
Somewhere in the LKML archive right now is a patch that would page your on-call SRE at midnight next Tuesday. Sashiko flagged it last month. You will never know which one it was.
That is what the new normal feels like from the inside.
Rust Won. Both Sides Quit.
On the same day the release landed, Miguel Ojeda pushed his final Rust-for-Linux pull request for 7.0 with a one-line sign-off.
“The experiment is done, i.e. Rust is here to stay.”
Four years ago, that sentence would have gotten him shouted at. Rust first landed in Linux 6.1 in late 2022 as an opt-in experiment, merged over objections from maintainers who thought it was a fad, a political project, or worse. Six releases later, the experimental tag comes off. Rust is a peer language in the kernel.
Individual subsystems still choose whether to accept Rust code, and the vast majority of the kernel stays C, but the argument is over. The Nova driver (NVIDIA’s open-source replacement for nouveau, targeting Turing architecture) ships with Rust code in 7.0. The Rust DRM infrastructure Danilo Krummrich has been building for two years is now mainline.
The people who spent four years getting it there are not in the room.
Wedson Almeida Filho led Microsoft’s Rust-for-Linux effort. After four years of arguing with C maintainers who did not want his code anywhere near their subsystems, he posted a resignation citing “nontechnical nonsense” and walked away. His co-lead Alex Gaynor stepped down the same week Rust received official status.
The victory lap happened without them.
On the other side, Christoph Hellwig maintained the DMA subsystem for twenty years. That is the kind of foundational code most engineers do not know exists because they never have to touch it. A year earlier he had called mixing Rust with C “cancer” in a public email. When maintainers agreed to let Rust drivers call C DMA APIs through a thin wrapper, Hellwig stepped down. Marek Szyprowski took over.
Twenty years. That is a person’s entire professional life, not just a chapter.
The final argument had nothing to do with technology. It was about whether a new language gets to call your functions through a wrapper. Hellwig lost, then chose to leave.
Safe Rust makes entire categories of bugs structurally impossible. Buffer overflows, use-after-free, null-pointer dereferences. These things cannot be written in safe Rust. The 23-year NFSv4 overflow Carlini’s script found is, by construction, something that cannot exist in safe Rust code.
The kernel now includes a language that makes the CVE from the beginning of this article impossible to write. And the people who fought for that are gone, and the person who fought against it is gone, and Linux 7.0 shipped anyway.
New Rules for AI-Written Code
The new rulebook shipped alongside the release.
Any patch written with AI help must now carry an Assisted-by: trailer naming the model and tools. AI agents cannot sign Signed-off-by lines, because the Developer Certificate of Origin is a legal claim only a human can make. Accountability for bugs stays with the human who pressed send.
This rule did not appear because the community sat down and wrote one calmly. It appeared because NVIDIA engineer Sasha Levin submitted a patch to kernel 6.15 that he had generated almost entirely with a language model, including the changelog, and did not tell anyone.
The code compiled. It passed initial review. It also contained a performance regression that survived into stable and ruined someone’s week.
The backlash was loud enough that Linus, who has no patience for process meetings, cut the debate short: calling for outright bans was “pointless posturing.” AI is a tool. Accountability lives with the human. Ship the policy.
Red Hat, which has been shipping commercial Linux longer than most developers in this story have been coding, raised a harder concern that has not yet been answered.
Language models trained on GPL-licensed code make it structurally hard to guarantee the provenance of any submission. Whose copyright is in the output? That problem is not solved by Linux 7.0. It is also not going away.
Linux 7.0 Hardware Legacy: From XFS Self-Healing to SPARC Survival
A RAID controller in a datacenter runs its SCRUB cycle overnight, the routine integrity check across every disk in the array. It flips a single bit inside the filesystem’s bookkeeping metadata. A 0 became a 1 where the kernel least wanted it.
If you run XFS (the default filesystem on RHEL, Rocky Linux, AlmaLinux, and Oracle Linux), you historically found out in one of two ways. Either a service started misbehaving, or you read xfs_repair output on an unmounted disk the next morning.
Neither makes for a good Monday.
Darrick J. Wong submitted version 6 of his XFS self-healing patchset on January 15, 2026, and it shipped in 7.0.
Before this release, if a file server at a mid-size company lost a single byte of filesystem metadata over the weekend, the on-call engineer got paged, drove in, took the server offline, ran xfs_repair, and brought it back up before Monday.
Best case: four hours of downtime. Worst case: the repair ran past the maintenance window, and the Monday status meeting started with an apology.
Linux 7.0 replaces that weekend drive-in. A background daemon called xfs_healer detects the same corruption, fixes it while the server keeps serving files, and writes to the system log. Users never notice. The pager stays silent. Monday starts on time.
Multiply by the cloud. XFS is the default on AWS, GCP, and Azure RHEL-family images. Most of the enterprise Linux fleet on the planet just got quieter.
Somewhere in a bank in Frankfurt, a SPARC M7 server is settling a trade. The software was written in 1998. The contract with Oracle says nobody moves it.
On April 12, that server got new kernel code. SPARC (Sun Microsystems, early 1990s vintage) received a fork/clone bug fix, new clone3 system call support, and API cleanups. DEC Alpha, which mostly lives in scientific labs where the simulation code was written when I was in high school, got a fix for user-space memory corruption during memory compaction. Motorola 68000 got patches too.
None of those readers are going to write a blog post about it. They will install the kernel and feel seen, somewhere at the back of the neck.
On April 7, the tip branch accepted the removal of Intel i486 support for Linux 7.1. The 486 shipped in 1989. The x86 32-bit code path is still widely used, and dropping i486 compatibility lets it run faster on everything that runs it today.
SPARC stays because someone cares enough to own it. The 486 is removed because no one cared enough to own it.
AMD’s newest server chip, the EPYC 9005 (the generation cloud providers are currently racking by the thousand), now runs encrypted virtual machines more efficiently under 7.0’s refreshed KVM path. Encrypted virtual machines are the feature banks and hospitals pay extra for so that the cloud provider itself cannot read their data. Benchmarks on modern EPYC 9005 “Turin” servers show SEV-SNP overhead in the single digits to low teens on memory-heavy workloads.
ML-DSA (Module-Lattice-Based Digital Signature Algorithm, the NIST-approved post-quantum standard) lands at three security levels: 44, 65, and 87.
Every time a Linux machine loads a driver, it checks a cryptographic signature to be sure the driver came from someone authorized. Today’s signatures can be forged by a quantum computer large enough to break them, and the machines to do that do not exist yet.
The problem is that hostile intelligence services are already recording encrypted signature traffic. When quantum computers are ready, they will decrypt what they recorded today. This is called “harvest now, decrypt later.” ML-DSA signatures today exist so that code signed in 2026 is not broken in 2035.
Linux 7.0 Gave AI Three Physical Keys
Three new keycodes landed in the input subsystem, submitted through the HID fixes pull request for 7.0 by Google, which authored both the kernel patch and the underlying USB-IF HID specification (HUTRR119).
KEY_ACTION_ON_SELECTION(0x254) triggers an AI action on highlighted content: explain, summarize, search.
KEY_CONTEXTUAL_INSERT(0x255) opens an overlay to generate or retrieve text into the active field.
KEY_CONTEXTUAL_QUERY(0x256) offers suggestions related to the selected element.
Unlike Microsoft’s Copilot key (a 2024 addition that hard-bound a repurposed legacy function key to one vendor’s assistant), these three are first-class HID values and explicitly agent-agnostic. A laptop vendor can map them to physical keys, Fn combinations, touchpad gestures, whatever.
The keyboard changed from an “input device” to a “device that invokes agents.” Not a metaphor. Kernel code.
One Linux 7.0 Release, Four Technical Shifts
In the same commit history, AI reviews kernel patches on the mailing list with a 53% catch rate. AI finds kernel bugs that had been hidden for 23 years. The kernel grew three physical keyboard keys dedicated to sending text to AI agents. As a side note, AI can now appear as a credited contributor under a new policy and tag.
Infrastructure built for AI, and infrastructure made safer by AI, arrived in the same week.
The Next 23-Year Bug
If one person with one bash script found five kernel vulnerabilities in a long weekend, how many has Google’s internal team found? How many has your hardware vendor’s internal team found? How many has a state-level actor already found, archived, and not told anyone about?
Linus called it the new normal. OpenSSL. GCC. Python. Postgres. Chromium. The ten-year-old microservice in your repo that has not been touched since the author left the company. They are all sitting somewhere with a 112-byte buffer and a 1,056-byte write that nobody thought to look for, waiting for the bash script that has not been written yet.
The action items are practical. Running NFS? Have you patched CVE-2026-31402? Running XFS? Pilot the self-healing daemon on staging first. Running AMD EPYC 9005? Benchmark your own workload before promising the business a savings number.
None of this is new. What is new is the urgency behind it.
The real question is: that code in your repo written before 2010, whose author is long gone, still running in production. What is your plan when someone points Claude Code at it?
“We have code review” is no longer an answer. Code review missed this one. For twenty-three years. Not because the reviewers were not trying. Because the tools changed.
Frequently Asked Questions
Does the Linux 7.0 NFSv4 vulnerability affect my servers?
If you run any Linux-based NFS service, yes. The patch for CVE-2026-31402 is already out. Whether you compile your own kernel or use a distribution package, check your patch status first. This vulnerability has been in the code since 2003, and the barrier to exploit it is low enough that a laptop on guest Wi-Fi can trigger it.
What does Rust in the kernel mean?
It means Rust is no longer experimental. It is a peer language to C. The Nova driver and Rust DRM infrastructure already ship with Rust code. However, only specific subsystems accept Rust so far, and the vast majority of the kernel remains C. For ordinary users, the short-term impact is minimal. Long-term, it means fewer memory safety bugs.
Does XFS self-healing need to be enabled manually?
xfs_healer is a background daemon in Linux 7.0. Whether it is enabled by default depends on your distribution’s packaging policy. RHEL-family distributions will likely enable it by default because it directly affects their SLA commitments. Validate it in staging before pushing to production.
Linus called it the new normal. You might not feel it yet, but Linux 7.0 has already written it into kernel code.
